ABSTRACT
Embedded wireless networks have largely focused on open-loop sensing and monitoring. To address actuation in closed-loop wireless control systems there is a strong need to re-think the communication architectures and protocols for reliability, coordination and control. As the links, nodes and topology of wireless systems are inherently unreliable, such time critical and safety-critical applications require programming abstractions and run time systems where the tasks are assigned to the sensors, actuators and controllers as a single component rather than statically mapping a set of tasks to a specific physical node at design time.
To this end, we introduce the Embedded Virtual Machine (EVM), a powerful and flexible programming abstraction where virtual components and their properties are maintained across node boundaries. In the context of process and discrete control, an EVM is the distributed run time system that dynamically selects primary-backup sets of controllers to guarantee QoS given spatial and temporal constraints of the underlying wireless network.
The EVM architecture defines explicit mechanisms for control, data and fault communication within the virtual component. EVM-based algorithms introduce new capabilities such as predictable outcomes and provably minimal graceful degradation during sensor/actuator failure, adaptation to mode changes and runtime optimization of resource consumption. Through case studies in process control we demonstrate the preliminary capabilities of EVM-based wireless networks.
EVM DESIGN FLOW
We now describe the design flow from control problem formulation, automatic translation of control models to platform-independent EVM inter preter based code and finally to platform-dependent binaries (see Fig. 3(a)). Therefore, a VT description is obtained using a parser that processes the Simulink model file by searching for a new block definitions along with the interconnections between blocks. An example of creation of a VT’s functional description from a Simulink design model in Fig. 3(b) is presented in Fig. 3(c). As the platform-independent language is stack-based, the notation is in reverse.
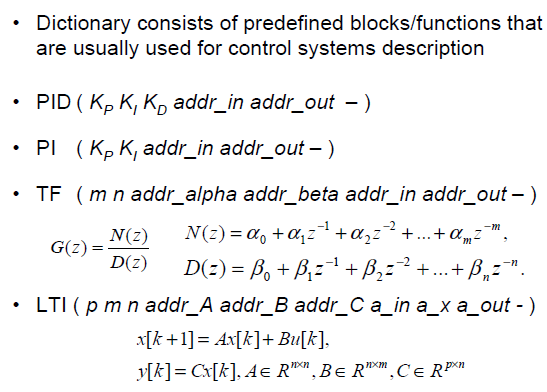
Figure 4. Control-EVM platform-independent and domain-specific
language for expressing functional and timing description of
Simulink models.
The use of the EVM intermediate programming language enables domain-specific constructs, where basic programming libraries are related to the type of application that is being developed. For example, for use in embedded wireless networks for industrial control, we developed two predefined libraries, Common-EVM, based on the standard FORTH library and Control-EVM that contains functionality widely used for developing control applications as shown in Fig. 4.
EVM ARCHITECTURE AND IMPLEMENTATION
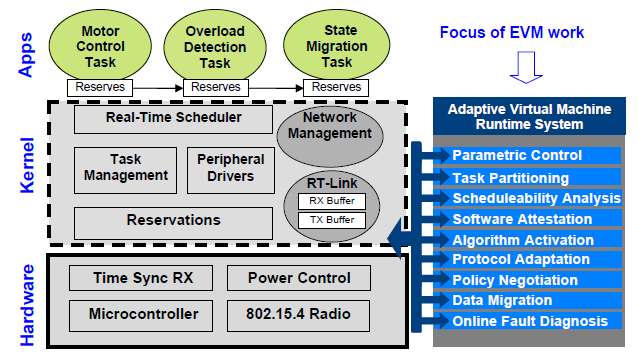
Figure 5. nano-RK RTOS architecture with EVM extensions.
nano-RK has been design as fully static OS, configured at the design time. Therefore to allow parametric and programmatic run-time changes in the code nano-RK was redesigned and extended with several new features (see Fig. 5).
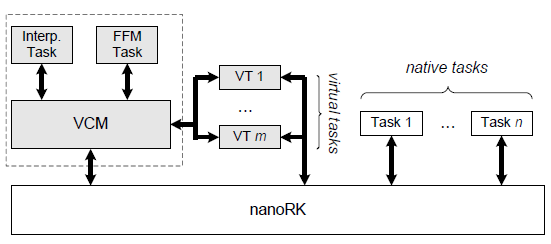
Figure 6. EVM architecture with Virtual Component Manager running as a supertask along side native nano-RK tasks.
The EVM run time system is built on top of the nano-RK real-time operating system as a super task, allowing node-specific tasks to execute natively and virtual tasks (VTs), i.e. those that are dynamically coupled with a node, to run within the EVM. The EVM services are shown in Fig. 5 and the EVM blocklevel reference architecture is presented in Fig. 6.
VIRTUAL TASK ASSIGNMENT
We now discuss the EVM algorithm for determining the best set of physical controller nodes to execute virtual tasks, given a snapshot of current network conditions. The goal of the assignment procedure is to determine: (1) Assignment of the control algorithms to the set of nodes V, where each VT is assigned to one node as a Primary and to R nodes as a Backup. (2) Communication schedule that determines active links at each time slot. Communication between nodes is scheduled using TDMA based protocol with frame size FS. (3) Computational schedule that determines in which time slot each control algorithm is executed. We first sketch the general formulation followed by a more intuitive relaxed formulation.
VIRTUAL TASK EXECUTION
When each VT is assigned with Primary and Backup nodes along with appropriate routing, the VC starts executing its VTs. The existence of multiple maximum node-disjoint paths allows more robust information flow with respect to a single failure. We are focused on system faults due to failures and not due to malicious behavior of nodes in the VC.
- Planned and Unplanned adjustments
- Schedulability Analysis
IMPLEMENTATION
To evaluate the EVMs performance in a real setting with multiple coordinated controller operations, we used a factory simulation module (FischerTechnik model factory). The factory consists of 22 sensors and actuators that are to be controlled in a coordinated and timely manner.
A block of wood is passed through a conveyor, pushed by a rammer on to a turn table and operated upon by up to three milling/cutting/pneumatic machines. The factory module was initially controlled by wired programmable logic controllers (PLCs). We converted it to use wireless control with FireFly nodes controlling all sensors and actuators via a set of electical relays.
CASE STUDY

Figure 7. Simulation of EVM behavior when used for ’Shell problem’ control; Nodes: green nodes-actuators, red nodes-sensors, blue circle-highlights Primary node, blue circle-highlights Backup node.
We have simulated the performance of the EVM for the case when a wireless network is used to control the Shell Problem, a well-known problem from the process control theory. Fig. 7(a) presents a Simulink framework used for the simulation, where the Controller (shown in Fig. 3(b)) and the Plant are similar to models. Fig. 7(b) presents the initial topology of the VC along with the Primary and the Backup nodes.
The system response to a series of different step inputs (a new one arrives every 60s) for the initial topology is presented in Fig. 7(d). If the initial topology changes after some of the links fail (as shown in Fig. 7(c) but without changing the position of the Primary and the Backup node), the system without the EVM, where only rerouting algorithms are used, will have a response presented in Fig. 7(e). Fig. 7(f) shows how the EVM’s adaptation to unplanned changes in link quality allow us to keep the system’s response similar to that in the initial topology.
RELATED WORK
There have been several variants of virtual machines, such as Mat´e, Syclla and SwissQM, and flexible operating systems, such as SOS[8], Contiki, Mantis, Pixie and LiteOS, for wireless sensor networks. The primary differences that set the EVM apart from prior work is that it is centered on real-time operation of controllers and actuators.
Within the design of EVM’s operating system, link protocol, programming abstractions and operation, timeliness is a first-class citizen and all operations are synchronized. The EVM does not have a single node-perspective of mapping operations to one virtualized processor on a particular node but rather maintains coordinated operation across a set of controllers within a VC.
DISCUSSION
We have investigated several fundamental challenges with the use of wireless networks for time-critical closed-loop control problems. Our approach was to build the networking infrastructure to maintain state across physical node boundaries so tasks are decoupled from the underlying unreliable physical substrate. We present an IP formulation of the run time task assignment problem and show that it is possible to compute task assignment efficiently and in a composable manner across concurrent control problems.
We implemented an initial version of the EVM infrastructure on commodity embedded nodes and demonstrated the capability in an all-wireless factory across 22 sensors/actuators. This paper presents an initial stab at a problem that unravels a series of problems at the heart of network Cyber-Physical Systems. The complexity of reaching consensus limits our current implementation a centralized architecture. Future work will focus on distributed and scalable wireless control networks.
Source: University of Pennsylvania
Authors: Miroslav Pajic | Rahul Mangharam
>> More Wireless Sensor Networks Projects Abstract for Engineering Students
>> More Wireless Embedded Projects for Engineering Students
